How To Find Ipv6 For Mac
What is the difference between the IPv4, IPv6, and MAC addresses of a device? Update Cancel. For Media Access Control. Where IP addresses are associated with TCP/IP (networking software), MAC addresses are linked to the hardware of network adapters. What is the difference between IPv4 and IPv6 in tabular form? Finding the IPv6 address of your Mac or iPad isn't extremely difficult. But there are a few technical wrinkles to be aware of. While OS X, with access to the command line and more disclosure in.
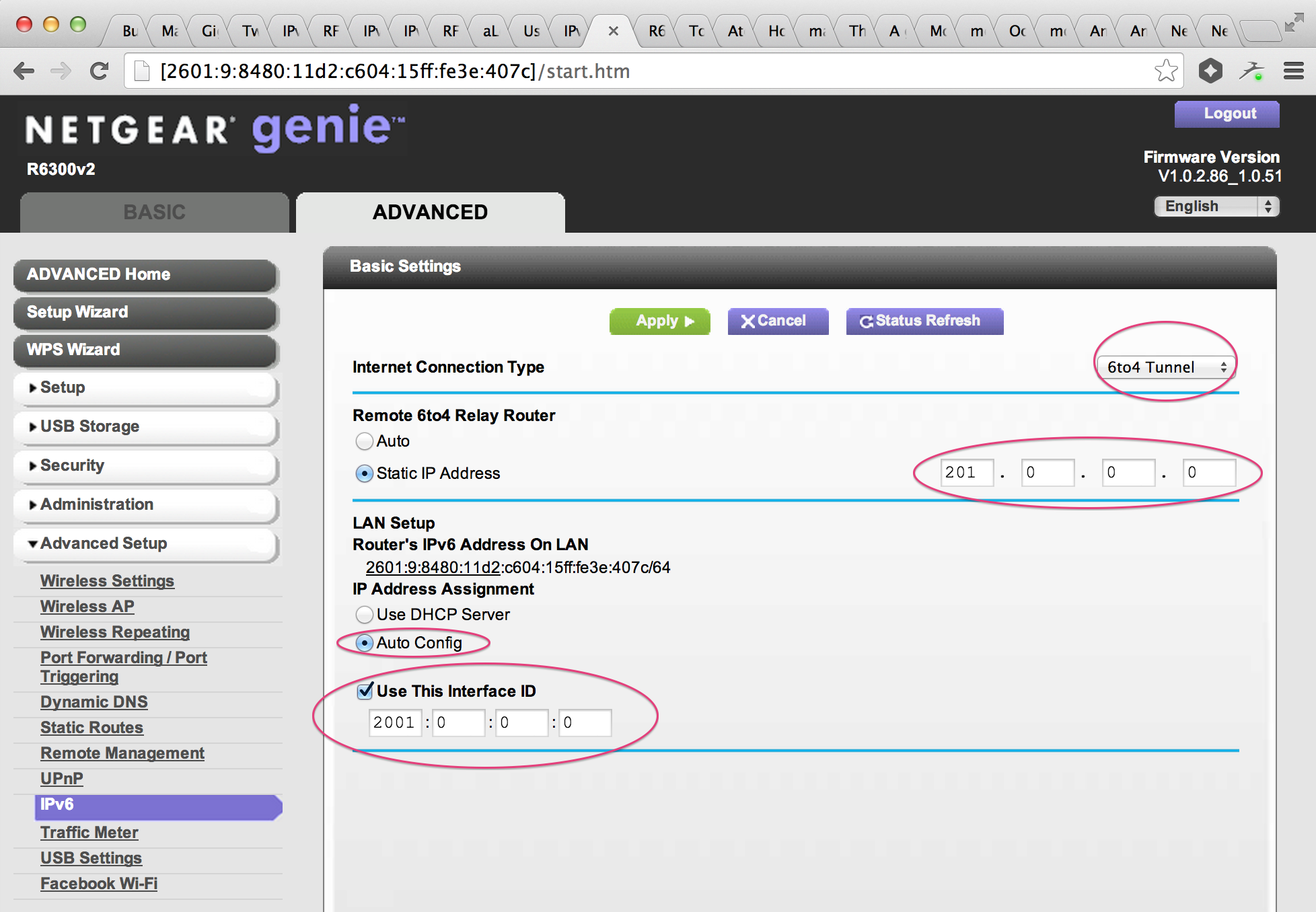
Otherwise go to the 'Search programs and files' box. • Type cmd.exe • In the cmd window, type ipconfig. Windows 7 GUI users: • Go to the start menu • Go to the control panel • Go to 'Network and Internet' • Go to 'View network status and tasks' • Go to 'Change adapter settings'. • Go to your main Internet connection, double click • Go to 'Details' • Look for 'IPv6 Address' and 'IPv6 Default Gateway' Other Windows based OS's: Send jfesler@test-ipv6.com detailed instructions; and I'll add them to the site. If you set up a tunnelbroker tunnel: The most common causes for tunnelbroker users to fail are: • Your IPv4 address may have changed; you need to tell the tunnelbroker server this happened. • If you are using your router to do the 6in4 (sometimes called 6to4 with explicit provider): • Make sure tunnelbroker knows your current IPv4 address. Our site tells you your public IPv4 address.
Links for Further Reading Here are a few links for further reading. Since my references for this article are always inline, I am only listing further links here: • Cisco DocWiki: • Insinuator: • D-Link: • My (detailed information about IPv6 attacks) Featured image “” by is licensed under. Email Address Categories • (3) • (4) • (18) • (1) • (8) • (1) • (4) • (97) • (9) • (20) • (47) • (33) • (15) • (3) • (3) • (2) • (1) • (186) • (11) • (10) • (5) • (34) • (15) • (3) • (42) • (45) • (3) • (5) • (27) • (9) • (6) • (7) • (3) • (9) • (64) • (11) • (4) • (12) • (1) • (9) • (7) • (159) • (4) • (34) • (1) • (29) • (12) • (5) • (28) • (2) • (20) • (51) • (1) • (2) • (2) • (9) • (2) • (1) • (3) • (1) Recent Comments • Srinivasan on • on • on • Sebastian on • Jerome on • Sebastian on • on • Sebastian on • on • on.
• See for more information on why you would want to switch; and some options. (IPv6 address: starts with FC or FD) ULA or Unique-Local-Unicast: If you have an IP address starting with FC or FD, you have what is effectively a private IPv6 address. It might be usable for talking to other devices within your home, or within your company. It also allows you to have a steady IPv6 address inside, even if your public IPv6 address changes regularly. The main problem with ULA is that certain home routers are now offering ULA, *and* giving you a default route.
Leading zeros must be removed. 2001:0db8::0001 must be written as 2001:db8::1. '::' must be used to represent the largest number of 16-bit sets of zero as possible. If there are multiple places where '::' can be used, and the numbers of zeros are the same, use '::' on the leftmost set of zeros '::' cannot be used to shorten a single 16-bit set of zeros. Letters in an IPv6 address should be written in lowercase. To represent port numbers, wrap an IPv6 address in square brackets then followed by a colon and the port number as [2001:db8::1]:80 For more information see.
• Make sure the box 'doing 6to4' can ping the other side of the tunnelbroker gateway before working on any other hosts. (IPv6 address: starts with 2002) If you use 6to4 (without a tunnel broker; ie, using anonymous 6to4): The use of 'automatic' 6to4, or the use of 6to4 without explicit configuration of the gateways, is not recommended. For more information see. If you want to continue trying to debug anonymous 6to4: • If you are using your router to do the 6to4: • Make sure your router has a public IPv4 address. Without this, 6to4 fails. • If your router permits you to log in, use 'ping' or 'ping6' and see if you can ping 'ipv6.test-ipv6.com'. Don't waste your time fixing computers until the router works!
To find mac from IPv6 can speak of how to from mac add convert an IPv6 a) in a mac example, 6c:20:56:3e:a7:c5 b) insert ff:fe in middle 6c:20:56:ff:fe:3e:a7:c5 c) reformat to IPv6 notation as 6c20:56ff:fe3e:a7c5 d) convert the fist octet from hex to binary 6c--> 0110 1100 e) invert the bit at index 6, continuing from 0 --> 01101001 [correct? ] invert the bit at index 6, continuing from 1 --> 01101111 [correct? ] invert the bit at index 6, continuing from 0 --> 01101000 [correct? ] f) convert octet back to hex: 69 or 6F or 68 [which one of three is correct ]?** g) replace first octet with newly calculated: 69 (6f, f8)20:56ff:fe3e:a7c5 h) prep-end link-local prefix: fe80::69 (6f, f8)20:56ff:fe3e:a7c5. To find mac from IPv6 can speak of how to from mac add convert an IPv6 You can calculate an IPv6 interface ID from a MAC address only in case the device uses SLAAC to build the IPv6 address from the ISP assigned IPv6 prefix (usually a /56 or /64) and the MAC address.
Instructions for your OS are below. When looking for your IPv6 address, skip any fe80: address. Everyone has them if their OS supports IPv6; this is regadless of whether or not your ISP supports IPv6 yet. Those are 'link local' addresses; used just for communicating to other hosts in the same physical network as you.
B) To find the mac with IPv6 simply depend on the last words of the IPv6 in Hex bytes showing me? Sincerely BleuOisou.
We decided to activate IPv6 on the guest/ Wifi. In this way, many users and clients will operate with IPv6 without touching the productive LAN. One of the first questions in this scenario was: How can we know which device had which IPv6 address at a given time? How can we trace back which device (user) has done some malicious actions when we only see many different “privacy extended” IPv6 addresses in the firewall log without any MAC addresses? Since we had no layer 2 switches that support first-hop security services such as neighbor discovery monitor or router advertisement guard, the idea was to use a host on the local network to sniff and “search” for new IPv6 addresses and their correspondent MAC addresses.
This forum is for help with Dyn's services only. For help with your Cisco R device you had to refer to Cisco support. So denfinely RotBlitz. Vista replaced once motherboard, the model having supported only one Mac address. Untrusted IPconfig / all gave two-Mac IPv4 with new motherboard while IPv6 in off board? Implying there is an IPv6 mac address device Used never installed by somewhere.
How To Find Ipv6 Prefix
The Ethernet frame is sent to an IPv6 multicast address (beginning with 33:33:) with a source MAC address of the IPv6 node, in this case an Apple device. The message has ICMPv6 type 135 and a “Target Address” of its tentative link-local IPv6 address (fe80::): The Tcpdump line for the same DAD message looks like that. 2014-01-06 13:30 b8:ff:61:4f:98:f4 > 33:33:ff:4f:98:f4, ethertype IPv6 (0x86dd), length 78: (hlim 255, next-header ICMPv6 (58) payload length: 24):: > ff02::1:ff4f:98f4: [icmp6 sum ok] ICMP6, neighbor solicitation, length 24, who has fe80::baff:61ff:fe4f:98f4 Tcpdump Script and Analysis I am dividing my method in two sections: At first, a Tcpdump runs in the background in order to store all DAD messages in a *.pcap file. For the subsequent analysis, the stored *.pcap file is read into a textfile which can then be analysed using grep, etc. For the capturing of IPv6 packets I recommend to use a second hardware interface on the Linux host which does not participate at layer 3 at all, i.e., has no IPv6 addresses: sudo sysctl -w net.ipv6.conf.eth1.disable_ipv6=1.
Please consider upgrading to Internet Explorer 8, 9, or 10, or trying another browser such as Firefox, Safari, or Google Chrome. (Please remember to honor your company's IT policies before installing new software!) • • • •.
The complete Tcpdump command which uses the second interface card on the host and creates a new *.pcap every day looks like that. Mergecap -w dad_2014-01-all.pcap /var/log/dad/dad_2014-01-* In the next step, tcpdump is used to read out the file and to write it into a textfile. I am using it with three more options: • “-e” to print the link-level header on each dump line. This reveals the MAC addresses. • “-n” to not convert addresses (i.e., host addresses, port numbers, etc.) to names.
Here is the result I got. For the geek at heart, we have the venerable command line.
DDNS helps to have the IPv4 but IPv6 on the Cisco R model. IPv6 in a static status into this R, dns as well the gateway IPv6 addresses. So, to test them, use the to find whose IPv6 all of detected by the R, that replied none of these IPv6 add with Location and Issuers!? IPv4 add of Wan been tested too, all replied loc and Publishers? A) Am using the R having IPv6 not by ISP directly? Or the IPv6 not public IPv6, but privacy ones?
Let’s start with the easiest. Chasing a live IPv6 address in the IPv6 world is similar to the IPv4 world: find the nearest router, browser the IPv6 NDP cache (rather than the IPv4 ARP cache) to find the MAC address of the ‘bad’ IPv6 host, then look in all switches for the specific MAC address. If the IPv6 address is no more active in the network, this becomes more complex in IPv6 even in the case where all routers send Router Advertisement (RA) messages with the M-flag which forces all DHCPv6-able hosts to use DHCPv6 and not stateless auto-configuration. Indeed, the DHCPv6 log does not contain the MAC address anymore for a specific IPv6 address but rather the DHCP Unique Identifier (DUID) which is unique per DHCPv6 host but is not always a MAC address; it can also be any number. The choice of DUID is done by the client, so, we can only hope that the majority of the DHCPv6 clients will use the MAC address as their DUID! [ ] If the host relies on stateless auto-configuration (DHCPv6 not enabled or not implemented), there are basically two cases: the easiest is when the host uses a single permanent EUI-64 IPv6 address and the most difficult is when the host has privacy extension (known as temporary addresses under Windows).
So if we have 4 subnetting bits, then we can create 2 4=16 new subnets.::1/128 is the loopback address.::FFFF:0:0/96 are the IPv4-mapped addresses. Fe80::/10 are the link-local unicast. 2001:db8::/32 are the documentation addresses. Ff00::/8 are multicast addresses Our includes IPv6. Correct IPv6 Notation IPv6 addresses should be written a certain way. This will make interpreting the addresses faster and easier, both for humans and for computer programs.
• If you are using your Linux, BSD, Mac, or Windows box to 'talk 6to4' specifically: • Make sure your router is passing 'protocol 41' to you. • Most home systems have private IPv4 addresses; this won't work with 6to4 (unless.) • Make sure your 6to4 interface knows your public IPv4 address. • Make sure that your router permits protocol 41 from any IP address - not just 192.88.99.1. This will allow web sites to operate their half of 6to4, even if they can not spoof the 192.88.99.1 anycast address. • Linux users using iptables connection tracking: take heed of the previous note! • Consider changing how you connect. • • Ask your ISP if they offer any IPv6 connectivity (including possibly 6in4 tunnels, or tunnelbroker type tunnels).
Ethernet has 'multicast' MAC addresses as well – any MAC address with the 'group' bit set is technically a multicast address; IPv6 uses the prefix 33:33:*, while IPv4 uses 01:00:5e:*. There are other widely-used prefixes, see for details.
Assuming you're on a wired connection, enter the command ~ ifconfig en0 You should see something like this: Lo and behold, those addresses are nicely labeled, and the one marked 'temporary' is your privacy address. It changes, depending on usage conditions. Leaving it the same for a week would make the machine too vulnerable; changing every few minutes would have a performance impact. From my reading, it ends up being updated every 24 to 72 hours.
Alternatives • Switch, Switch, and again: Switch: It should be clear that countermeasures for layer 2 attacks or layer 2 monitoring at all should be deployed on the layer 2 infrastructure as well. A passively sniffing host (such as used in this PoC) will not see everything on the network but mostly “broadcast” messages. That is, the concept of first hop security in the switches is the answer for these situations.
If you are the network administrator: You can use the default route information to identify the ethernet address; and then search for the owner of that ethernet address. Some network vendors have features that will suppress the advertisements of unauthorized RAs (router announcements); consider enabling those feaatures. More reactive measures involve finding (by ethernet address) the owner of the device; or possibly spoofing RA's from their device to indicate the device is going away. Consider trying the 'netalyzr'. This is another site that runs a java applet (which can do more than my site can, in just javascript).
The network you are on may intentionally offer IPv6; you'll automatically use it when your computer sees it. Where this goes wrong: Some people plug their router into the network (wired or wireless) and inadvertantly offer IPv6 services to everyone.
Specific Windows features depend on IPv6 being enabled. • To completely disable IPv6 (Windows 7, Vista; XP should be similiar): • Go to the start menu • Go to the control panel • Go to 'Network and Internet' • Go to 'View network status and tasks' • Go to 'Change adapter settings'. • Go to your main Internet connection, double click • Go to 'Properties' • Uncheck 'Internet Protocol Version 6' • Hit 'ok' • Shutdown/reboot.
It would require a sniffer in every subnet to completely cover the whole network. • Not against “real” attackers: This method only fits for normal users that might unintentionally do some malicious actions.
We would like to show you a description here but the site won’t allow us. Brett michael still dating taya, online adult video chat for mac.
It will not work for the capturing of MAC addresses from hackers who could omit the DAD message or simply change their hardware MAC address at all. • If DAD fails for the IPv6 node: Consider the really rare situation in which an IPv6 node wants to register an IPv6 address that is already used. This is no problem for the node since it generates another one. However, in the DAD logs, the DAD message for this (already used) IPv6 address appears with the MAC address of the new IPv6 node. On a subsequent analysis of the DAD logs, this IPv6 address could misleadingly point to the MAC address that did not get this address.
To disable IPv6 in Windows XP: • Taken from: • Make sure you are logged in as an Administrator. • Click Start, click All Programs, click Accessories, and then click Command Prompt. • At the command prompt, type: netsh int ipv6 uninstall and press the Enter key on your keyboard. • Close the Command Prompt window and restart the computer. Other Windows based OS's: Send jfesler@test-ipv6.com detailed instructions; and I'll add them to the site.
Ipv6 Converter Padded Mac Address
In ipv4 addresses I can achieve this using ioctl(mac_arp_sock, SIOCGARP, &areq); as ARP doest not work in IPv6 what is the best way to retrieve the mac address of peer machine just by knowing peer IPv6 address? Well like the name says, SIOCG ARP uses the which is IPv4 only. And like the wiki page mentions: the Neighbor Discovery Protocol is its successor. So, previously you could use ioctl with SIOCGARP or 'arp -a' which used the same backend. And now you have to start a subprocess / task 'ndp -na' and parse its stdout which looks like: Neighbor Linklayer Address Netif Expire St Flgs Prbs fd00::xxxx:b1ff:xxxx:fc25 b8:xx:b1:xx:fc:xx en0 permanent R R xxxx::ca2a:xxxx:fe56:xxxx%en0 xx:2a:xx:56:xx:cc en0 23h17m41s S fe80::xxxx:14ff:xxxx:ca52%en0 c8:xx:14:xx:ca:xx en0 23h17m40s S See reference: Advanced: Google for the implementation of ndp e.g. BSD/OpenBSD/src/usr.sbin/ndp/ndp.c if you want to implement it your self without using the ndp-command.
What's behind this is that the way a device gets its IPv6 address can vary. It might be self-assigned or it might be assigned to the device. A device can get away with self-assigning its own IPv6 address because of the vast, and I mean vast, number of IPv6 addresses available: 2 128 = 3.4 x 10 38. For example, one could assign every square centimeter on the surface of Earth a million different IPv6 addresses each and every second for the next million years and still not exhaust the full 2 128 bit address space. (That's a simplification, actually, because the IPv6 address space is segmented for different uses, just like IPv4, but you get the idea.) There is a protocol for self-assignment, and it has continued to evolve. For some time now, OS X and its sibling iOS have used what's called the EUI-64 address.
I've exchanged some email with Mr. Hamilton, and he really knows his stuff. On the Interfaces tab, under 'en0, Wi-Fi Interface,' IPv6 Toolkit displays the IPv6 addresses provided to it by the iOS kernel. Again, you can look for the 'ff:fe' string that earmarks the EUI-64 address so that you can uniquely identify the other one, the privacy address. Perhaps a future version of the app will have explicit labels.
Motherboard drivers for hp pavilion. Here is the list of ASRock Motherboard P4i65GV Drivers we have for you. To Download ASRock Motherboard P4i65GV Drivers you should Download Our Driver Software of.
OS X users: To find your IP address using the GUI: • Go to the 'Apple' menu (top left corner) • Go to System Preferences • Go to Network • Click on your primary network (green icon) if you have more than one work. • Go to 'Advanced' • Look at the TCP/IP tab, uder 'Configure IPv6'. • Make a note of whether or not there is a router. • Make a note of the IPv6 address (if any). OS X users: To find your IP address using the command line: • To open your terminal: Go to your Applications folder; go to Utilities; and double click Terminal.
Other routers: Try updating the firmware. If that fails, disable IPv6 entirely on the router. 2005:123:456:789: WRVS4400N routers: Disable IPv6.
Over time, that practice raised concerns about privacy, and so the concept of a second, parallel 'privacy address' or 'temporary address' has developed. OS X started using the privacy address starting in 10.7 Lion, so that's why you see two IPv6 addresses on the TCP/IP tab. How can we tell which is which? Apple hasn't bothered to label the two IPv6 addresses, so we have to do a little work on our own. The first thing to note is that an EUI-64 address an embedded string 'ff:fe' near the middle, so look for that.